Use Case Description
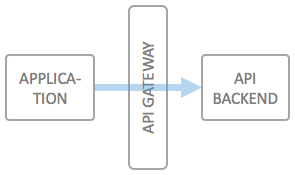
One of the most basic use cases for an API Gateway is to enable simple machine to machine API access, including self service aspects for the developers needing access to a specific service. The special case for machine to machine communication is that usually no end user is part of the communication, or that the an end user's identity and rights have been established up front.
Typical examples of services which leverage machine to machine type communication are backend services which deliver value for other applications, such as licensing services, product management services or other types of data management systems which are either intended for pure backend purposes or for which the client applications are trusted to have already authorized an end user for using it.
These types of APIs can either be secured using
- API Keys, or
- OAuth2 Client Credentials
From a security perspective, the methods are more or less identical, and it's a matter of taste whether you want to leverage the very simplistic "API Keys" approach, or the standard OAuth2.0 flow, which exchanges client credentials for an access key.